Criminals offer reporter money to hack BBC

Joe TidyCyber Reporter, BBC World Service
 BBC
BBCLike many things in the shaded world of cyber crime, a threat coming from inside is something that there are very few people experience.
Fewer people want to talk about it.
However, when I was suggested by a criminal gang myself, a unique and worrying experience was given about how the computer pirates could benefit from inside people.
“If you are interested, if you provide us with access to your PC, we can offer you 15% of any ransom payment.”
This was the message I received from a blue from someone named Syndicate at the encrypted chat application signal in July.
I had no idea who this person was, but I immediately knew what it was about.
If I helped cyber criminals access BBC systems through my laptop, a potentially large amount of money was offered.
They would steal the data or install malware and hold my employer as a ransom, and I will secretly take a cut.
I’ve heard stories about such things.
In fact, just a few days before the unwanted message, he said that the entrance details of a IT worker there from Brazil there was a pirates of the computer, which the police said that he said that he had lost $ 100 million (£ 74 million) for his banking victim.
After receiving advice from a senior BBC editor, I decided to play with Syndicate. I was willing to see how criminals made these shaded agreements potentially with treacherous employees at a time when cyber attacks in the world became more effective and destructive for daily life.
I told SYN, who changed its current name, I was potentially interested, but I should know how to work.
They announced that if I gave them my login information and security code, they would hack the BBC and then force the company for a ransom in Bitcoin. I would line up for some of this payment.
They increased their offers.
He said: “We are not sure how much BBC pays you, but if you have received 25% of the last negotiation because we have issued 1% of the total income of the BBC?
SYN predicted that the team could demand tens of millions of ransoms if they have infiltrated the company.
The BBC has not received a public position as to whether to pay pirates, but will not pay advice from the National Crime Agency.
Nevertheless, the computer pirates continued their fields.
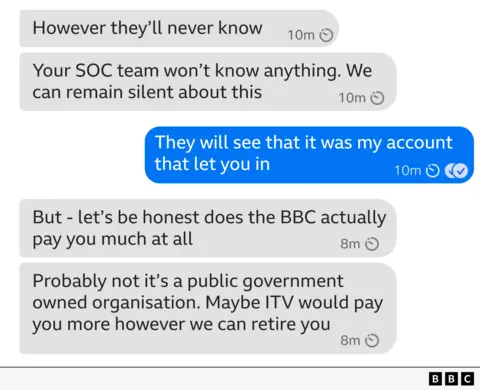
Syn said I would be millions of rows. “We will delete this conversation so that you can never find it,” they insisted.
Hacker claimed that they were very successful with striking agreements with the inside attacks.
The names of the two companies hacked this year were shared as an example of when an agreement with an UK health company and an US Emergency Service provider was shot.
“You will be surprised by the number of employees who will access us.” He said.
Syn said it was a “lying manager” for the cyber crime group Medusa. He claimed that he was the only British speaker in the western and gang.
Medusa is a ransom software operation as a service. Any criminal workplace can register for the platform and use it to interrupt organizations.

According to a research report from the checkpoint of the Cyber Security Company, it is thought that Medusa’s managers operate outside Russia or one of the allied states.
“The Group avoids targeting organizations in the Russian and Independent Society and [its activity is predominantly] Russian Dark Web Forums. “
Syn proudly sent me a link Public Opinion warning about the US Medusa It was released in March. US Cyber officials, the group is active in four years, “more than 300 victims” hackled, he said.
SYN insisted that they were serious in making a agreement to secretly sell to my company’s kingdom for a heavy payment day.
You never know who you were talking to, so I asked him to prove Syn. “You may be a messy kids or someone who tries to trap me,” I suggested.
They responded to Medusa’s Darknet with a link and invited me to contact them through the Tox of the band, which is a safe messaging service loved by cyber criminals.
Syn was very impatient and increased the pressure to me to answer.
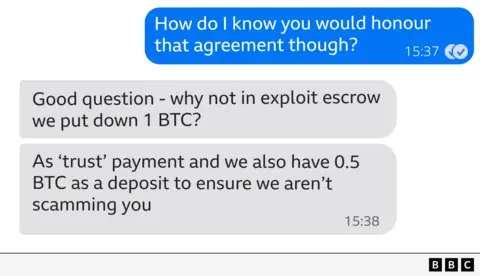
They sent a link to the recruitment page in a special Cyber Crime Forum, which called for a 0.5 Bitcoin (about $ 55,000) in a deposit arrangement of Medusa to start the process of securing the process.
After delivering my login information, they guaranteed me at least this money.
“We do not bluff or we do not joke – we do not only have a purpose for money and money, and one of our main executives asked me to reach you.”
Apparently they chose me because they assumed that I was technically intellectual and had a high level of access to BBC CT systems. I’m still not sure that SYN knows I’m a cyber reporter, not cyber security or CT employees.
Even if I knew about the BBC IT network, they asked many questions that I wouldn’t answer. They then sent a complex computer code confusion and asked me to run it as a command on my work laptop and to report what he said. They wanted to know which built -in CT access once I had to start planning.
At this point, I had been talking to Syn for three days and I decided that I was going forward enough, and I needed extra advice from the BBC’s information security experts.
It was Sunday morning, so my plan was to talk to my team the next morning.
That’s why I stopped for time. But Syn was uncomfortable.
“When can you do this? I’m not sick,” Hacker said.
“I think you don’t want to live on the beach in Bahamas?” They put pressure.
They gave me midnight on Monday. Then your patience is over.
My phone started ping with two -factor authentication notifications. Pop-ups came from the security entry application that asked me to confirm that I was trying to log in on my BBC account of the BBC.
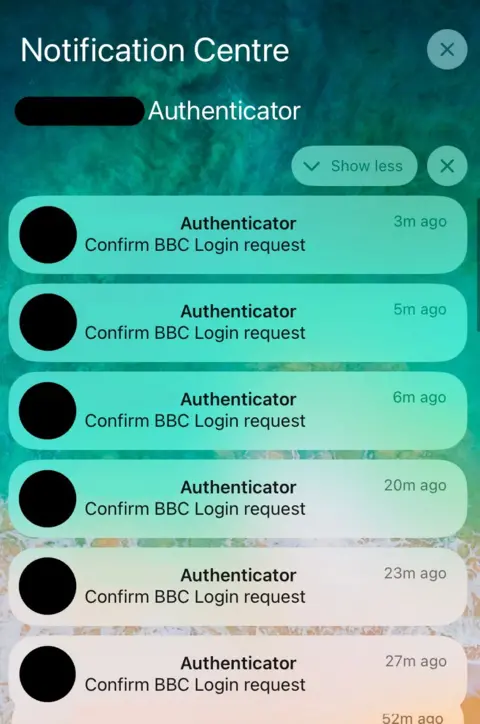
While holding my phone in my hand, the screen is full of a new desire every minute.
I knew exactly what this was – a hacker technique known as MFA bombing. The attackers bomb a victim with these pop ups by trying to log in from an unusual device.
Eventually sacrifice accidentally accepts pressure or eliminates pop-ups. How is this celebrity UBER Hacked in 2022.
It was disturbing to be at the end of the buyer.
Criminals, the security of my chat application was relatively professional conversation on my phone home screen. I felt like criminals playing my front door aggressively.
I was confused in tactical change, but I was too cautious to open my conversations with them if I accidentally accepted. This would immediately access the computer pirates to my BBC accounts immediately.
The security system would not be as malicious as it seemed to be a normal entry or password reset from me. After that, the computer pirates could have started looking for access to sensitive or important BBC systems.
As a reporter, not a CT worker, I did not have a high level of access to BBC systems, but still meant that my phone could not be used in an alarming and effective way.
I called the BBC Information Security team and as a precaution, we agreed to separate me from the BBC. No e -mail, no intranet, no internal vehicles, no privilege.
The strange quiet message from the computer pirates arrived later that evening.
“The team apologizes. We were testing your BBC login page, and we are very sorry if this causes you any problem.”
Now I explained that I was locked and uncomfortable with the BBC. Syn insisted that the agreement was still there if I wanted. But after they did not answer for a few days, they deleted their signal accounts and disappeared.
In the end, there were additional guards to my account, but I was restored to the BBC system. And with the experience of being involved in a threat attack from inside.
It is an insight that emphasizes the entire risk area for organizations that I really do not appreciate until the continuous intervention of cyber criminals and the organizations I don’t really appreciate until the receiving end.