New FileFix attack targets Meta accounts with fake security warnings

NEWNow you can listen to FOX News articles!
Cyber criminals continue to find new ways to target social media users, and meta accounts continue to be one of the most common charm. Losing access to Facebook or Instagram may have real consequences for both individuals and businesses, which can increase the likelihood of falling into urgent security warnings. The attackers use it by sending convincing notifications that force you to activate quickly without thinking.
This is exactly what makes the new file campaign so dangerous; It looks like routine account care, but it’s really a trap.
Sign up for my free Cyberguy report
Get my best technology tips, emergency security warnings and special opportunities delivered directly to your incoming box. Also, you will instantly access my final fraud survival guide – Cyberguy.com/newsletter
False Microsoft Warnings How to deceive you to your identity hunting scammers?
Cyber criminals target Facebook and Instagram accounts by sending false security warnings. (FOX News)
How does the file attack work?
As reported by the researchers in Acronis, a leading cyber security and data protection company, the attack starts with an ID hunting page that appears to be a message from the meta’s support team, and claims that your account will be disabled within seven days unless you view a “event report”. Instead of providing a real document, the page hides a malicious powershell command as a file path.
The victims are instructed to copy, open the file traveler and stick to the address bar. Although it may seem harmless, this action secretly runs the code that initiates the process of malware infection.
This method is part of an attack family known as Clickfix, where people are deceived by gluing their commands into system dialog boxes. Filefix, created by Red Team researcher Mr.D0X, creates this idea by using the file traveler address bar instead. In this campaign, the attackers developed cheat by hiding the malicious command behind the long space series, so only a fake file path can be seen for the victim.
A hidden script then downloads what looks like a JPG picture from Bitbucket, but the file contains the embedded code. After being executed, it removes another script and dissolves the last load password and skips many security tools in the process.
Falling identity hunt for this bank cheat cheat
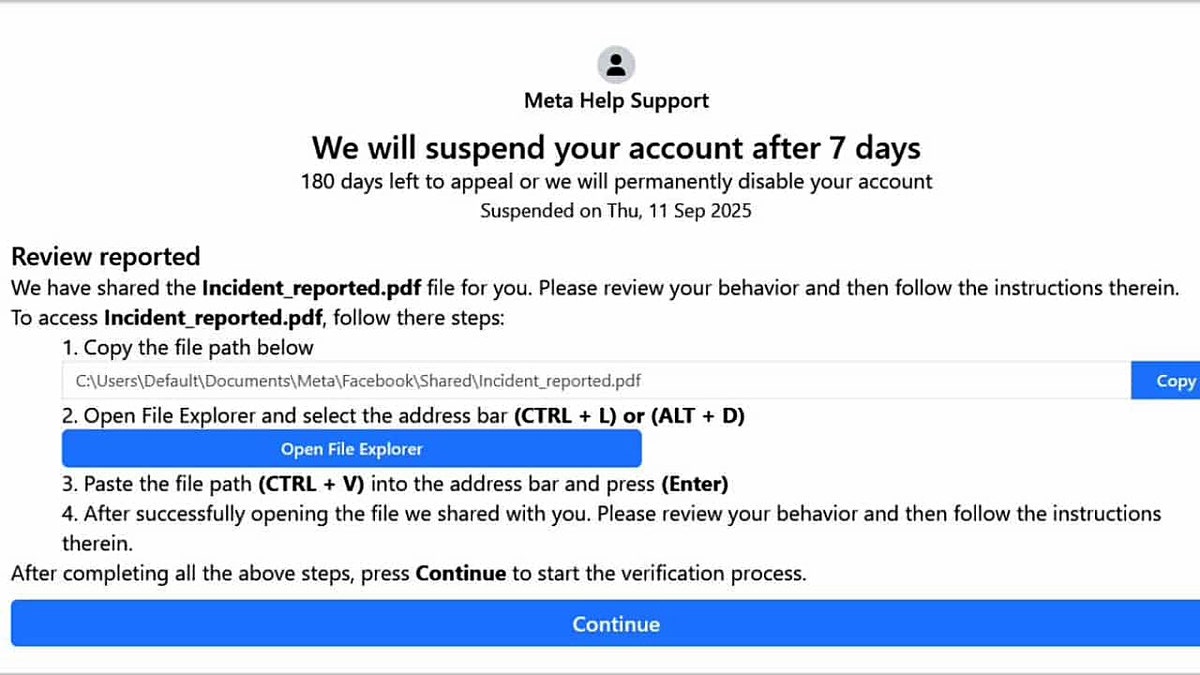
Filefix sends fake warnings that call on users to examine account security. (Aconis)
What stealc tries to play
The malicious software offered by this campaign is Stealc, an infostealer that collects a wide variety of personal and organizational data. Chrome is designed to get browser identity information and authentication cookies from Firefox, Opera and other browsers.
It also aims at messaging applications such as Discord, Telegram and Pidgin as well as crypto currency wallets such as Bitcoin, Ethereum and Exodus. Stealc goes further by trying to compromise on VPN services such as Amazon Web Services (AWS) and Azure, Protonvpn, and even Battle.net and Ubisoft. In addition, the victim can take the screenshots of the desktop and give the attackers a vibrant appearance of sensitive activities.
Acronis reported that the campaign appears in several different versions for a short time and that there were changes in the infrastructure and infrastructure. This shows that attackers actively test and develop their methods to prevent perception and improve their success rates.
Meta deletes 10 million Facebook account this year, but why?

Stealc also targets VPN software and crypto currency wallets. (Istock)
5 ways to protect yourself from Filefix attacks
In order to avoid attacks such as files and prevent malicious software such as Stealc, you must combine the warning with practical security measures. The following steps can help protect accounts, devices and personal data.
1) Be skeptical for emergency warnings
The attackers rely on panic. Treat any message that claims that your commodity account or other services will be disabled carefully. Instead of clicking links or tracking instructions on an E -Post or web page, verify the warning directly through official platforms.
2) Avoid copying commands from unknown sources
Filefix is based on persuasion to bond the hidden Powershell commands hidden as file paths. Do not make commands to system dialogues, files or terminals unless you are absolutely not sure.
3) Invest in personal data removal services
Filefix and Stealc improve information they can remove from a device or connected accounts. By using data removal services, you reduce the amount of sensitive personal information that can be found online or exposed on old platforms. This minimizes what attackers can use if they manage to achieve access.
Although no service can ensure that your data can be completely removed from the Internet, a data removal service is a really smart choice. They are not cheap and not your privacy. These services do the whole job for you by actively monitoring your personal information from hundreds of websites and systematically deleting it. This is what gives me peace and proves that your personal data is the most effective way to delete it from the internet. By limiting the existing information, you will make it difficult for scammers to target you by reducing the risk of crossing the cross -reference, the risk of obtaining from violations with the information they can find in dark network.
Take a look at my best choices for data removal services and visit a free scan to find out if your personal information is already on the web Cyberguy.com/Delete
Get a free screening to find out if your personal information is already on the web: Cyberguy.com/freescan
4) Upload reliable antivirus software
A strong antivirus software can detect malware such as Stealc before it is completely executed. Many solutions now contain behavioral -based detection that can mark suspicious scenarios or hidden downloads, and attackers help to capture threats even when they try to conceal commands as harmless actions.
The best way to protect yourself from malicious connections that uploaded malware that accesses your private information is to have a strong antivirus software on all your devices. This protection can warn you about identity hunting and ransom software fraud by keeping your personal information and digital assets safe.
Get my choices for the best 2025 antivirus protection winners for your Windows, Mac, Android and iOS devices Cyberguy.com/Lockupech
5) Use a password manager
When targeting stored identity information, using a reputable password manager reduces the risk by creating unique passwords for each site. In this way, even if a browser or application is endangered, the attackers cannot access your accounts elsewhere.
Then see if your E -mail has appeared in past violations. Our password administrator (see Cyberguy.com/passwords) includes a built-in violation browser that checks whether your e-mail address or passwords appear in known leaks. If you discover a match, replace the redeveloped passwords immediately and secure these accounts with new, unique identity information.
Check out the password managers for the best expert in 2025. Cyberguy.com/passwords
Click here to get the Fox News app
Wolf’s key takeaway
Cyber criminals continue to find creative ways to deceive social media users, and Filefix proves how these frauds can be convinced. A fake meta warning may feel urgent, but it is the best defense to pause before clicking or copying anything. It is superior to relying on strong habits and safety tools. Data removal services, antivirus software and password managers reduce the risk in different ways. When you combine them, you make it much more difficult for the attackers to turn a scary tactic into a real threat.
Should platforms such as meta do more to warn users about these developing identity hunting tactics? Type us by writing to us Cyberguy.com/contact
Sign up for my free Cyberguy report
Get my best technology tips, emergency security warnings and special opportunities delivered directly to your incoming box. Also, you will instantly access my final fraud survival guide – Cyberguy.com/newsletter
Copyright 2025 Cyberguy.com. All rights reserved.




